Kronos for Mac 1.8 Minecraft Download Updated
Kronos for Mac 1.8 Minecraft Download
Last updated on January 17, 2021 at xvi:00 CST (-0600)
Rumble tin can assist you lot build an upward-to-date asset inventory and search for assets that may be afflicted by the contempo spate of Log4J vulnerabilities (e.k. Log4shell, etc.). You lot can and so share the results with your security team for investigation and mitigation.
Rumble is not a vulnerability scanner. At this stage, vulnerability scanners have limited coverage, and are unable to detect all variants with a normal scan. Updates will eventually be available, merely until then, Rumble's asset inventory can help you get ahead of the event.
Log4j vulnerabilities
Cyberspace discussion was abuzz on December 9th virtually an 0-mean solar day vulnerability that tin yield remote code execution (RCE) in Apache's pop Log4J logging library for Java. This particular vulnerability — tracked as CVE-2021-44228 with the maximum "critical" CVSS score of ten — resides in Log4J's lookup adequacy, combined with JNDI (Java Naming and Directory Interface). This upshot is widespread because many developers were unaware that Log4J was unsafe to use with unfiltered input.
The most significant bear on is that an attacker tin can cause a cord to reach the logger, that when processed past Log4J, executes arbitrary lawmaking. The first examples of this used the ${jndi:ldap} path, which could lead to arbitrary code beingness loaded from a remote URL. This path is partially mitigated past the use of newer Java runtimes that block the URL-based grade loader past default. Unfortunately, a modern version of Java may not be enough to preclude exploitation, every bit the application itself may expose classes that tin can be used to run capricious lawmaking.
While Apache released fixes to CVE-2021-44228 in Log4J version two.15.0, information technology was discovered these fixes were "incomplete in certain not-default configurations", allowing for exploitation in sure circumstances (tracked as CVE-2021-45046 (with a "critical" CVSS core of 9.0), leading to a Log4J 2.16.0 release to address CVE-2021-45046.
Post-obit that release, a new vulnerability was raised which can yield a denial-of-service set on via infinite recursion. Tracked equally CVE-2021-45105 (and with a "loftier" CVSS score of 7.5), this vulnerability appeared to bear upon Log4J versions two.viii through the well-nigh recent 2.16.0 release, and was fixed in versions ii.17.0 (for Java 8) and 2.12.three (for Coffee vii).
Then on December 28th, security researchers at Checkmarx published findings of another RCE present in Log4J 2.17.0, one which requires the aggressor have permissions to update the logging configuration and, when successful, can yield RCE. Tracked as CVE-2021-44832 (and with a "medium" CVSS score of 6.vi), Apache released a set for this latest vulnerability in Log4J versions 2.17.one (for Java 8 and later), 2.12.4 (for Java 7), and 2.three.2 (for Java 6).
The broad popularity of Log4J—coupled with the relative ease of exploiting this vulnerability—creates potential conditions for far-reaching exploitation (like to Shellshock).
Google's security team have scanned the contents of Maven Primal and constitute over 35,000 affected packages, amounting to over 8% of those in the repository. Any application making utilise of the affected packages as dependencies may be vulnerable.
Affected applications include Elastic Search, Elastic LogStash, GrayLog2, Minecraft (client and server), Neo4J, many Apache projects (Druid, Dubbo, Flink, Flume, Hadoop, Kafka, Solr, Spark, Struts, Tapestry, Wicket), many VMware products (Horizon, vCenter, vRealize, HCX, NSX-T, UAG, Tanzu), Grails, and dozens if not hundreds of others. Log4J versions since two.0 are reported to contain this vulnerability, which was originally disclosed to Apache several weeks ago by the security team at Alibaba Deject.
The U.South. Cybersecurity and Infrastructure Security Agency (CISA) recently created a repo for tracking products/applications affected past Log4Shell, which will likely become the most reliable, long-term source-of-truth. We will keep to update this blog post while CISA builds out their listing.
Annotation: Rumble components–cloud platform, cocky-hosted, explorer, and CLI scanner–are not affected by this outcome.
Mitigations
Patches were made available to prevent code execution Log4J version ii.fifteen.0, merely these patches did not disable inline message lookup, which tin can betrayal things like environs variables and organization configuration settings to an attacker that can detect the generated logs. Additional patches were made available in Log4J version 2.16.0 to brand JNDI lookups disabled by default, express to certain protocols, and only localhost allowed by default. Further patches have been made in Log4J version two.17.0 to protect from uncontrolled recursion via cocky-referential lookups, along with additional patches in Log4J version 2.17.1 for limiting JNDI data source names to the java protocol.
For mitigations that folks can take immediately, Apache has offered some guidance.
Notation: Initially it was thought that the trouble could be mitigated by setting log4j2.formatMsgNoLookups or the environment variable LOG4J_FORMAT_MSG_NO_LOOKUPS. Apache have now clarified that those mitigation strategies are bereft.
Mitigating these issues requires i of the following deportment:
- Upgrading your Log4J version:
- This will remediate all recent known vulnerabilities.
- Log4J v2.17.1 or higher (for Coffee viii users).
- Log4J v2.12.iv or higher (for Coffee seven users).
- Log4J v2.three.ii or higher (for Coffee 6 users).
- Removing the JndiLookup course from the jars in the classpath:
- This just mitigates CVE-2021-44228 and CVE-2021-45046.
- NOTE: that this mitigation is non valid for Log4J version 2.sixteen.0.
$ zip -q -d log4j-core-*.jar org/apache/logging/log4j/cadre/lookup/JndiLookup.class - Overriding the
org.apache.logging.log4j.core.lookup.JndiLookupform by making appropriate changes to your classloader configuration:- This simply mitigates CVE-2021-44228 and CVE-2021-45046.
It is worth noting that an updated version of the Java runtime is not a sufficient mitigation. Newer versions of Coffee cake the URL class loader by default, but can yet be abused to leak secrets from the environment, and deserialization attacks may nonetheless succeed using classes already loaded past the procedure.
How to find applications that employ Log4J with Rumble
Identifying every awarding, device, and service using the Log4J library is going to be an ongoing attempt for security professionals. We will continue updating this post and our pre-built queries as more than data becomes available.
The following query tin exist used to place applications that are likely to exist affected by this outcome:
product:atlassian or product:avaya or production:coldfusion or production:coyote or product:cpanel or product:druid or product:"rubberband search" or production:"epolicy orchestrator" or product:flink or product:graylog or production:hadoop or product:horizon or product:imc or product:jamf or product:jboss or product:jetty or (production:"kerio connect" and protocol:http) or product:logstash or production:metabase or product:minecraft or production:mongodb or product:neo4j or product:openfire or product:pega or product:recoverpoint or product:resin or product:rundeck or product:symantec or product:sonicwall or product:solarwinds or product:sophos or product:splunk or product:tableau or product:tomcat or product:="ubiquiti unifi" or product:"vmware horizon" or production:"vmware vcenter" or product:"vmware vrealize" or product:"vmware site recovery" or production:vmanage or product:wowza or hw:netapp or hw:imc or hw:"ucs manager" or hw:"crosswork son apparatus" or hw:"site recovery manager" or hw:sonicwall or tcp_port:8983 or tcp_port:9092 or tcp_port:7077 or tcp_port:5347 or protocol:cassandra or protocol:elasticsearch 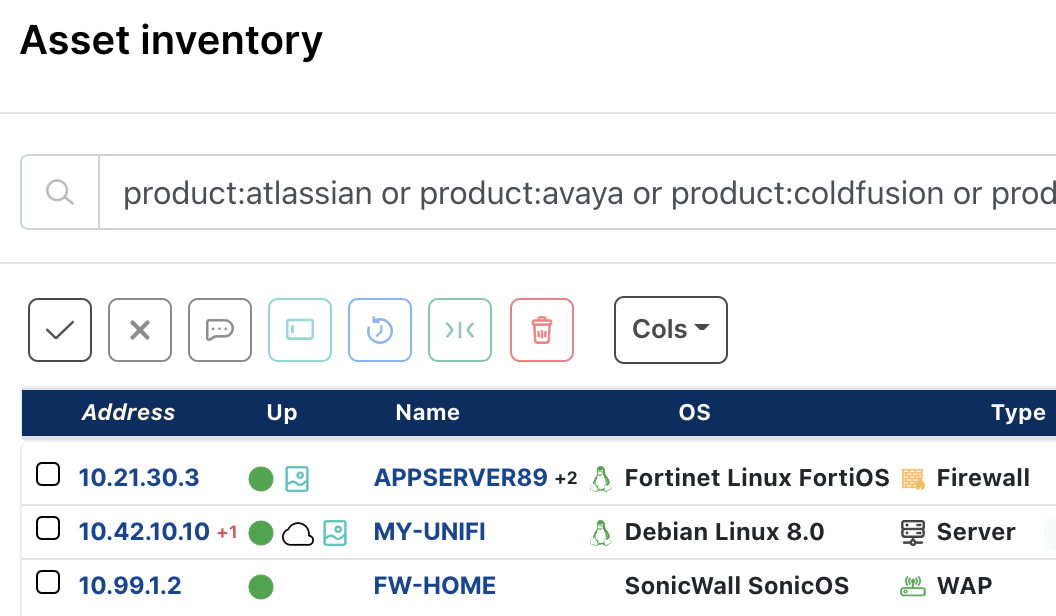
As always, any prebuilt queries nosotros create are available from our Queries Library. Check out the library for other useful inventory queries. Self-hosted customers may re-create the query above, or use the Export System Queries option to download an importable query set from the cloud console.
Kronos for Mac 1.8 Minecraft Download
Posted by: grosvenorables1990.blogspot.com
